External Attack Surface Scan.
Report in 24 Hours.
Find exposed domains, risky services, and leaked credentials before an attacker does. Delivered as a risk-scored PDF report. No platform, no vendor lock-in.
One-time scan. No subscription. No platform access required.
Who It's For
Security & Risk Teams
Answer the question your board is asking — what are we exposed to, and is it getting better? Get a snapshot of your internet-facing footprint with findings prioritised by risk.
MSPs & Pen Test Firms
White-label reports under your brand. You handle the client relationship, we handle the scanning and reporting. Add attack surface review to your service catalogue without building the tooling.
Compliance Teams
Evidence for auditors and regulators. Track your external exposure quarter-on-quarter and demonstrate remediation progress with documented, time-stamped scan results.
What it Finds
External Exposure
- exposed subdomains and forgotten environments
- internet-facing services and open ports
- subdomain takeover opportunities
High-Risk Interfaces
- admin panels (Jenkins, Grafana, Kibana, etc)
- cloud storage exposures (S3, Azure blobs)
- sensitive files and paths (.env, .git/, config dumps)
Network Services
- risky ports publicly reachable (RDP, databases, SSH)
- cleartext protocols in use (FTP, Telnet, HTTP)
- TLS weaknesses and expiring certificates
Email Security
- missing or permissive SPF records
- unenforced or absent DMARC policy
- DKIM configuration gaps
Known Vulnerabilities
- CVEs correlated to detected service versions
- CVSS-scored and publicly documented exploits
- vulnerability script indicators from port scan data
IP Reputation
- Spamhaus RBL listings (spam sources, compromised hosts)
- AbuseIPDB abuse confidence scoring
- botnet and exploit activity indicators
Default Credentials
- default credential testing against discovered services
- web admin panels, FTP, SSH, Telnet, databases
- screenshot evidence of authenticated access
Web Vulnerability Scan
- hundreds of checks against live web endpoints
- misconfigurations, exposed panels, known CVEs
- severity-scored findings with remediation
TLS Deep Analysis
- deprecated protocol detection (SSLv2/3, TLS 1.0/1.1)
- known vulnerabilities (BEAST, POODLE, Heartbleed, ROBOT)
- weak and export-grade cipher identification
JavaScript & Public Code
- JavaScript files scanned for hardcoded secrets and API keys
- public GitHub repositories searched for leaked credentials
- verified secrets reported as Critical findings
Remote Access Portals
- internet-facing VPN and remote access portals identified
- covers Citrix, Fortinet, Pulse Secure, GlobalProtect, RD Web, and more
- risk context including known CVEs and active threat actor targeting
Lookalike & Phishing Domains
- registered domains visually similar to yours detected
- covers typos, homoglyphs, character substitutions, and Cyrillic variants
- phishing and business email compromise risk assessment
Technology Fingerprinting
- web technologies identified across all live endpoints
- CMS, frameworks, servers, and identity providers detected
- version-level detail to support CVE and EOL tracking
How It Works
1. Scope
Submit your domain or IP range via the request form. No credentials, no access, no agents required.
2. Scan
We run the full scan — subdomain enumeration, port scanning, web probing, vulnerability checks, credential and secret scanning. Operator-driven, not automated noise.
3. Deliver
You receive a PDF and HTML report with risk-scored findings, evidence, and clear remediation guidance. Typically within 24 hours of payment.
What You Get
- full external asset inventory (domains, IPs, services)
- risk-scored findings with evidence
- screenshots of exposed and authenticated admin interfaces
- CVE correlation against service fingerprints
- default credential testing with screenshot proof
- email security posture (SPF, DMARC, DKIM)
- IP reputation and RBL listing status
- exposure drift tracking (what changed since last scan)
- clear executive summary and prioritised remediation
- web vulnerability scan across all live endpoints
- TLS deep analysis (deprecated protocols, known exploits)
- JavaScript and public repository secret detection
- remote access portal identification (VPN, Citrix, RDP, and more)
- lookalike domain detection for phishing and BEC risk
- technology stack fingerprinting across all web endpoints
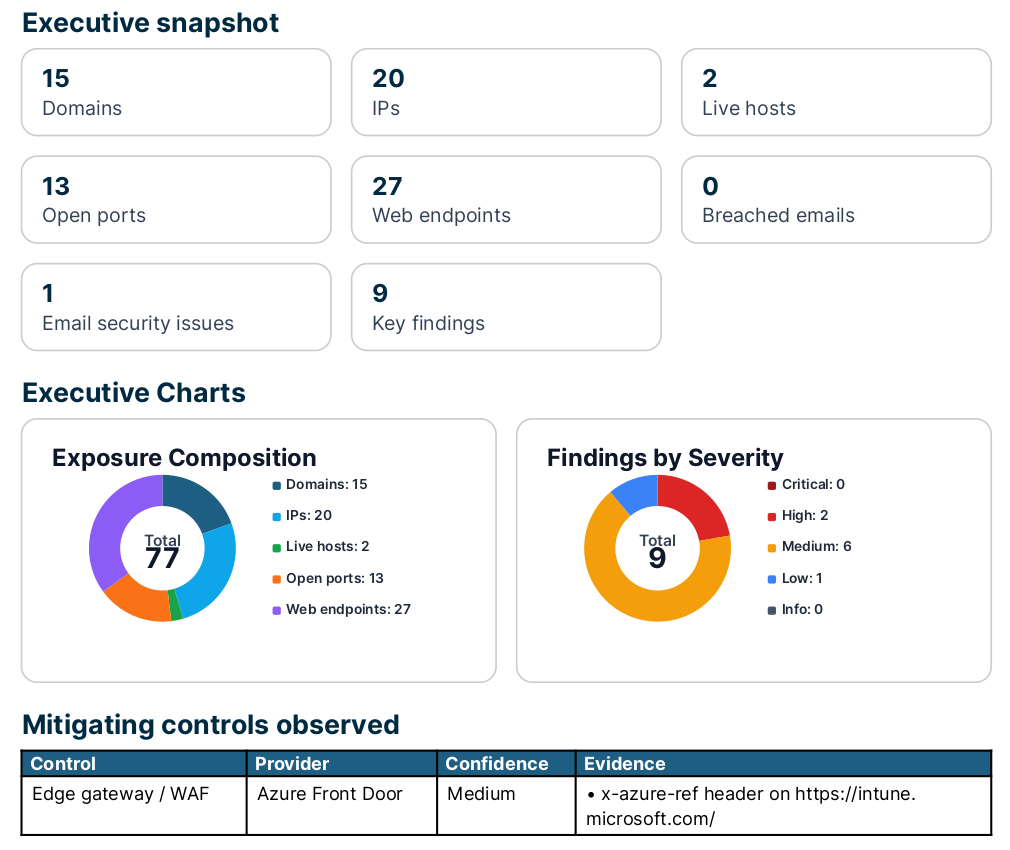
Example Report
A full sample report with realistic findings — see exactly what you'd receive.
Pricing
No subscriptions. No platform fees. Pay per scan.
Single Scan
- full external attack surface scan
- all findings categories included
- risk-scored PDF and HTML report
- evidence, screenshots, remediation guidance
- delivered within 24 hours
Quarterly Package
4 scans per quarter (~$187/scan)
- everything in Single Scan
- trend reporting — see what changed each month
- remediation tracking across scans
- direct email access to discuss findings
- suitable for compliance and risk reporting
Partner / Resale
Minimum 4 scans per quarter
- white-label reports under your branding
- you manage the client relationship
- we handle all scanning and reporting
- suitable for MSPs and pen test firms
- strong margins — charge clients $229+ and keep the difference
Ready to see what your organisation exposes to the internet?
Submit your domain. We'll handle the rest and have a report back within 24 hours.
Common Questions
The scanning process typically takes a few hours, run by an operator to ensure accuracy rather than automated noise. You receive the PDF report within 24 hours of payment confirmation.
Yes. Nmap, Shodan, and similar tools are freely available. Doing it properly — enumeration, CVE correlation, secret scanning, TLS analysis, typosquat monitoring — takes 40–80 hours of skilled time. SurfaceMapper automates the legwork and delivers it as a report. You're paying for time, not tools.
All findings are reviewed before delivery. We don't send a raw tool dump — every finding in the report has been assessed for relevance. No noise, no false positives.
No. All scans are passive and read-only. We observe only what is publicly visible from the internet. Reports are static files delivered to you. We don't retain scan data beyond the engagement.
A single scan is a point-in-time snapshot at $229. The quarterly package runs 4 scans over 3 months (~monthly cadence) for $749 — around $187/scan, saving roughly $165 versus buying them individually. On top of the saving, the quarterly package includes trend reporting across scans, remediation tracking, and direct email access to discuss findings. It's particularly useful for compliance reporting and board-level risk communication.
No. This is reconnaissance and discovery — identifying what is exposed and what is misconfigured from the outside. Penetration testing is active exploitation: attempting to use those exposures to gain access. They complement each other. SurfaceMapper is a good first step before commissioning a pen test, so you know where to focus.
No. SurfaceMapper does point-in-time scans. For 24/7 continuous monitoring, enterprise ASM platforms (Censys, Runzero, and others) are better suited. SurfaceMapper is the pragmatic alternative for organisations that don't need or can't justify an enterprise ASM budget.
We report it with clear remediation guidance and prioritise it at the top of the report. If anything is actively dangerous we'll flag it immediately rather than waiting for the report to be delivered. Actioning findings is your team's decision — we're not a managed remediation service.
Yes. The partner programme provides white-label PDF and HTML reports under your branding. You manage the client relationship, we handle the scanning and reporting. Email info@surfacemapper.net to discuss.
Domain and IP inventory, risk-scored findings with evidence, exposed services and admin interfaces, cloud storage exposures, email security posture, IP reputation, CVE correlation, TLS configuration analysis, JavaScript secret scanning, public repository credential scanning, technology fingerprinting, lookalike domain detection, and remote access portal identification. See the sample report for a full example.
Built by a Security Professional
Built by an Offensive Security Professional
SurfaceMapper was built by an offensive security practitioner, not a SaaS company. The scanning logic, finding logic, and risk scoring reflect how real attackers approach external reconnaissance — because it was designed by someone who does that work professionally.
Multiple CVEs published · Penetration testing and red team engagements across finance, healthcare, and critical infrastructure · External attack surface reconnaissance is part of the day job
